Petshop Pro
/ Update
1 min read
Easy | Web
ctf url: https://ctf.hacker101.com/ ↗
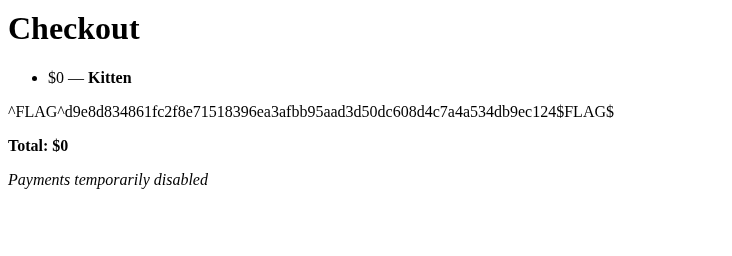
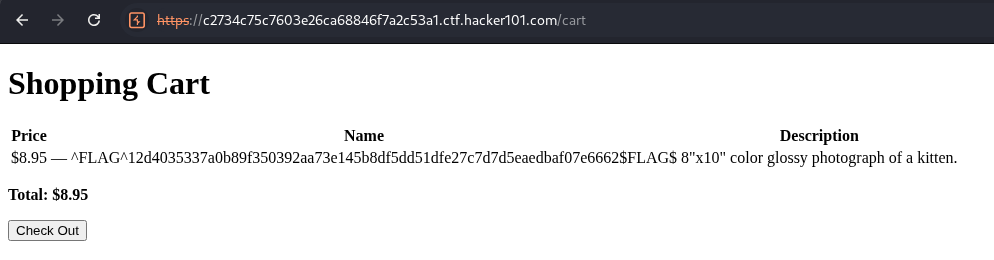
Flag 1#
- Inspect /cart.
- We see hidden input field containing item details
- POST /checkout content
URL encoded:
cart=%5B%5B0%2C+%7B%22name%22%3A+%22Kitten%22%2C+%22desc%22%3A+%228%5C%22x10%5C%22+color+glossy+photograph+of+a+kitten.%22%2C+%22logo%22%3A+%22kitten.jpg%22%2C+%22price%22%3A+8.95%7D%5D%5DDecoded JSON array:
[
[0, {
"name": "Kitten",
"desc": "8\"x10\" color glossy photograph of a kitten.",
"logo": "kitten.jpg",
"price": 8.95
}]
]- Change item price to 0 in burp or the hidden input field
we get 1st flag in the checkout page
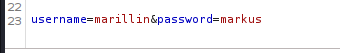
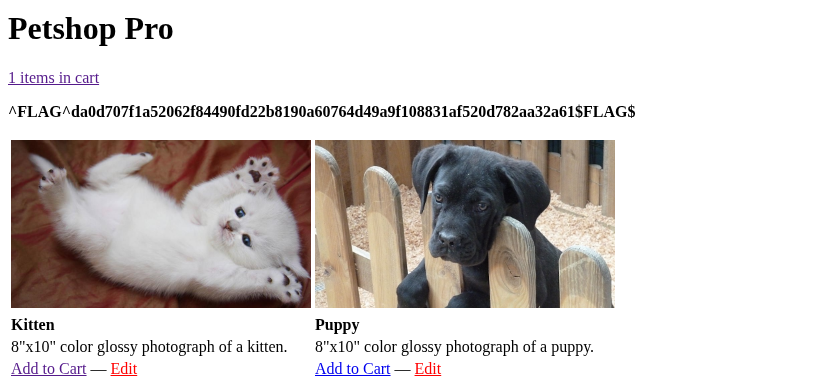
Flag 2#
- Fuzz url to find other pages
- found admin page login at /login
- Bruteforce credentials using hydra or fuzz or burp turbo intruder
- used names.txt ↗ from seclist
Flag 3#
Try XSS in item name
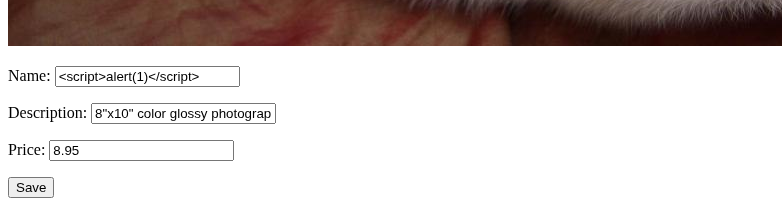
Go to cart
Petshop Pro
https://nahil.xyz/vault/writeups/hacker101/petshop-pro/
Author Nahil Rasheed
Published at September 28, 2025
Copyright
CC BY-NC-SA 4.0
Disclaimer This content is provided strictly for educational purposes only.